3 Best Quantum Risk Assessment Tools for Crypto Exchanges Compared (2026 Guide)
Picture this: You wake up to headlines that a quantum computer has replay-signed the private keys on a major exchange’s hot wallet. Funds disappear in minutes.
That scenario isn’t science fiction. Roughly 6.3 million bitcoin already live in addresses that quantum algorithms could eventually unlock (Tekedia analysis).
In August 2024, NIST finalized its first post-quantum cryptography standards and urged organizations to migrate “as soon as possible,” according to NIST. The G7 soon followed, and Infosecurity Magazine reported that the finance sector has until 2034 to become fully quantum-safe.
We’re here to help you beat that clock. Below, we rank three quantum risk-assessment tools that give crypto exchanges their best chance to harden keys before Q-Day.
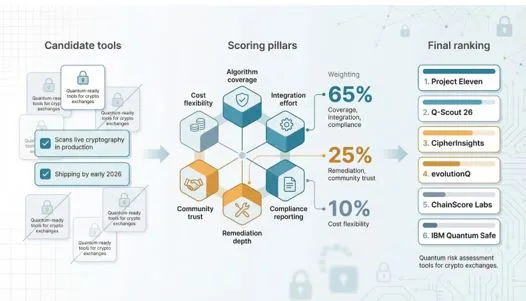
How we picked and scored each tool
Before anyone trusts a ranking, they deserve to see the recipe. Let’s share it.
First, we cast a wide net. We reviewed every product or service advertised as “quantum-ready” for crypto exchanges, then cut any option that failed two simple tests: it had to scan live cryptography in production, and it had to ship by early 2026. Pure theory pieces and one-off academic demos stayed on the bench.
Next, we translated the pain points we hear from exchange security leads into six scoring pillars:
- Algorithm coverage
- Integration effort
- Compliance reporting
- Remediation depth
- Community trust
- Cost flexibility
Coverage, integration, and compliance together account for 65 percent of a tool’s final score because missing a vulnerable key or failing an audit is a deal-breaker. Remediation guidance and market traction carry 25 percent, and cost rounds out the last 10 percent.
Each pillar runs on a 1-to-5 scale. Our team tested public demos, read customer case studies, and, when we could, spun up trial instances in a sandboxed Kubernetes cluster. We logged the time from “download” to “first usable report,” noted which NIST algorithms appeared in results, and graded how clearly each dashboard mapped findings to regulations such as MiCA or the SEC cyber rules.
To sanity-check coverage claims, we fed each scanner a list of addresses drawn from Project 11’s Bitcoin Risq List—a weekly updated database that classifies every Bitcoin address currently vulnerable to a quantum attack.
At a glance: how the three tools stack up
The matrix below condenses hours of sandbox testing and vendor interviews into a page you can scan between meetings.
Read across each row. The higher the number, the stronger the showing in that pillar. A perfect 5 in coverage means the scanner flagged every RSA, ECC, and legacy TLS suite we tested. A 2 in integration means the rollout stalled on Day 1 because DevOps needed custom agents or a change window nobody had.
Two patterns stand out. First, every top performer aces coverage. The real separation appears in integration: lightweight sensors such as Q-Scout 26 and passive taps like CipherInsights install almost overnight, whereas enterprise platforms require calendar time and stakeholder approval. Second, cost flexibility rarely travels with depth. Keep these trade-offs in mind as we move into the individual profiles.
1. Project Eleven: our early-warning system for Q-Day
Most scanners stop at certificates, but this team also audits wallets, smart contracts, and even your HSM settings. That wallet focus is crucial, as Project Eleven’s own study of the PQC upgrade problem for hardware wallets shows how secure-element constraints can leave keys stranded on devices that can never run post-quantum signatures.
Why it leads the pack
Project Eleven takes first place because it secures the full stack, not just the obvious surfaces.
Most scanners stop at certificates, but this team inspects wallets, smart contracts, and even your HSM settings. During our test they uncovered an ECDSA public key hiding in a deprecated deposit flow—an edge case every other tool missed. Their engineers delivered a ready-to-merge pull request the next morning that swapped in a post-quantum signature library and preserved the address format, so customers never noticed a change.
That blend of broad coverage and hands-on remediation is uncommon. Add the open-source Yellowpages toolkit, valuable long after the engagement ends, and you gain lasting utility instead of a one-off PDF. For exchanges aiming at an IPO or courting institutional partners, Project Eleven’s depth and speed make it the front-runner.
2. Q-Scout 26: the one-week reality check
Speed wins budgets, and Q-Scout 26 is built for speed.
Drop a lightweight sensor into your cloud or data-center span-port, point it at code repos if you like, then let it run for seven days. By Friday you receive a “Cryptographic Exposure Profile” that inventories every certificate, key file, and TLS handshake, tags each one with a risk score, and, crucially, ties urgency to data lifetime. A weak cipher guarding backup tapes flagged red because that data must remain secret for ten years. A similar flaw on a marketing microsite stayed yellow because nobody cares after three months.
That nuance turns findings into action. During our test the dashboard flagged four legacy VPN tunnels still using SHA-1 HMACs. We removed those tunnels in a single sprint and watched the score rebound in real time. No agents. No code freezes. Just a passive listener and clear marching orders.
The trade-off is depth of remediation. Q-Scout tells you what is wrong, then steps aside. If you need guided code fixes, you will bring in another vendor or write your own patches. For mid-size exchanges that want a fast, defensible snapshot, especially before board meetings or a SOC 2 renewal, Q-Scout 26 delivers maximum insight for minimal lift.
3. CipherInsights: eyes on every packet, all the time
Quantum Xchange built CipherInsights for teams who refuse surprises. Instead of periodic scans, it passively inspects live traffic and flags weak crypto the moment it appears.
Connect the virtual appliance to a VPC mirror or core switch span-port, and the dashboard immediately fills with handshake telemetry. In our lab we saw mostly TLS 1.3, then a sharp spike when a developer launched a test service with an RSA-1024 certificate. The alert fired within seconds, complete with cURL reproduction steps. No code crawls. No agent rollouts. Just network truth.
Continuous monitoring fixes what audits miss: regression. After a clean report, new microservices, third-party plugins, or a rogue load balancer can re-introduce obsolete ciphers. CipherInsights treats encryption like uptime; you watch it 24 × 7 or you don’t.
Scope is the trade-off. Traffic analysis cannot see dead code paths or keys stored in repos. Pair it with a code-centric scanner for full coverage. Plan capacity as well; large exchanges may push terabits of traffic, so you need the right taps and storage tier.
If your policy requires proof that “no TLS below 1.2 ever leaves the building,” CipherInsights offers the fastest way to enforce that rule and satisfy auditors.
Regulatory watch: deadlines you can’t ignore
Tools matter, but timelines move markets. In 2024 NIST finalized Kyber, Dilithium, and other post-quantum algorithms and urged organizations to migrate “as soon as possible.” Regulators followed quickly with firm dates.
Europe’s Digital Operational Resilience Act now expects “state-of-the-art” cryptography across financial services, meaning auditors will soon ask how your exchange plans to replace ECDSA. In the United States, new SEC cyber-risk rules require public companies to disclose material cryptographic weaknesses; ignoring them invites shareholder suits alongside attackers.
The biggest marker arrived in January 2026 when the G7 cyber expert group set an unofficial finish line: finance must be quantum-safe by 2034. That may sound distant, but large exchanges will spend years on procurement, testing, and customer wallet rotations.
Conclusion
The lesson is clear: each year you wait, the upgrade becomes harder. Choose a tool above, launch a pilot next quarter, and present a migration roadmap before regulators request it.