How Incident Response Planning Has Become a Boardroom-Level Conversation

The Evolution of Incident Response in Corporate Strategy
In today’s digital landscape, cybersecurity threats have escalated in both frequency and sophistication, making incident response planning an essential priority not only for IT departments but also for corporate boards. What was once considered a technical issue handled exclusively by IT professionals has now emerged as a critical component of overarching business strategy. This shift underscores the increasing recognition that cyber incidents can have severe financial, reputational, and operational impacts on organizations.
The growing importance of cybersecurity governance is reflected in the fact that 68% of companies worldwide experienced at least one cyberattack in the past year, with an average cost of $4.35 million per breach. As a result, boards are actively engaging in incident response planning to safeguard their enterprises, ensuring that strategies are robust and aligned with business objectives.
Moreover, the increasing complexity of cyber threats-from ransomware attacks to supply chain compromises-has pushed incident response beyond reactive measures. Organizations now emphasize proactive strategies, including threat intelligence sharing, vulnerability assessments, and continuous monitoring. This evolution demands that boards understand not only the technical aspects but also the broader business implications of incident response, making it a strategic conversation at the highest levels.
The Role of Technology Partners in Strengthening Incident Response
Key to this boardroom-level focus on cybersecurity is the involvement of specialized technology partners who bring expertise and managed services to the table. For instance, iMedia Technology in the industry plays a pivotal role in helping businesses design and implement proactive incident response frameworks. Their services often include continuous monitoring, threat detection, and rapid response capabilities that are vital in minimizing the impact of cyber incidents.
These technology partners also assist organizations in conducting post-incident analyses to identify root causes and prevent future breaches. By leveraging the experience and advanced tools of these external experts, companies can accelerate their response times and improve their overall security posture. The partnership also helps in aligning incident response strategies with regulatory requirements and industry standards, ensuring compliance and reducing potential legal liabilities.
Similarly, organizations benefit greatly from collaborating with firms like Cantey Tech, a professional IT firm, which offers tailored IT solutions and strategic advisory services. These partnerships enable companies to bridge gaps between technical teams and executive leadership, fostering a unified approach to incident management. By leveraging external expertise, boards can better understand risk exposures and compliance requirements, facilitating more informed decision-making.
Such collaborations often extend to training and simulation exercises, where technology partners facilitate tabletop scenarios that test an organization’s readiness. These exercises provide valuable insights to the board and management, identifying weaknesses in communication, coordination, and technical defenses. Ultimately, these partnerships elevate incident response from a purely operational activity to a strategic priority embedded in corporate governance.
Why Incident Response Is a Board-Level Concern
Several factors have driven incident response planning into the boardroom spotlight. First, regulatory pressures have intensified, with governments worldwide imposing stricter cybersecurity and data protection mandates. For example, the European Union’s General Data Protection Regulation (GDPR) and the U.S. Cybersecurity Maturity Model Certification (CMMC) require organizations to demonstrate effective incident response capabilities or face significant penalties.
Compliance is no longer just a checkbox exercise; it influences investor confidence and market reputation. Boards are increasingly held accountable for lapses in cybersecurity governance, with some jurisdictions introducing legal liabilities for directors and officers in cases of negligent oversight. This heightened scrutiny compels boards to be proactive participants in incident response planning rather than passive recipients of IT updates.
Furthermore, the financial consequences of cyber incidents have become too substantial to ignore. According to a report by Accenture, companies with well-prepared incident response plans reduce the cost of cyberattacks by an average of 35%. Boards recognize that investing in preparedness not only mitigates risk but also protects shareholder value.
Beyond direct costs, organizations face indirect expenses such as regulatory fines, legal fees, and increased insurance premiums. Cyber insurance is becoming a critical part of risk management, but insurers often require evidence of mature incident response capabilities before underwriting policies. Boards must ensure that incident response plans meet these evolving standards to maintain adequate coverage.
Additionally, the reputational damage from data breaches can erode customer trust and market position. High-profile breaches have shown that inadequate response can lead to long-term brand erosion, impacting customer loyalty and revenue streams. Research indicates that 60% of small and medium-sized businesses close within six months of a cyberattack due to reputational and financial damage. Consequently, boards are prioritizing incident response planning as a vital risk management function, integrating it into enterprise risk frameworks and crisis management protocols.
Bridging the Gap Between IT and the Boardroom
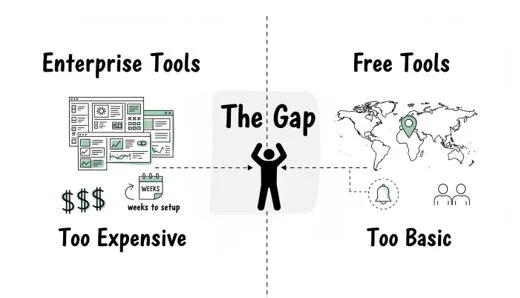
Despite growing awareness, a communication gap often exists between IT teams and board members. IT professionals may use technical jargon and focus on intricate details, whereas board members seek clear, business-oriented insights. This disconnect can hinder effective incident response planning and decision-making.
To address this, companies are adopting structured communication strategies that translate technical risks into business implications. Incident response plans are now presented in board meetings with clear metrics, scenario analyses, and impact assessments. This approach empowers boards to allocate resources appropriately and endorse necessary investments in cybersecurity infrastructure.
For example, dashboards summarizing key performance indicators (KPIs) such as mean time to detect (MTTD) and mean time to respond (MTTR) provide boards with tangible measures of incident response effectiveness. By contextualizing these metrics within potential financial and reputational outcomes, boards can better appreciate the urgency and scale of cybersecurity investments.
Training and awareness programs for board members further enhance their ability to engage in meaningful dialogue about cybersecurity risks. By understanding the evolving threat landscape and incident response best practices, boards can better fulfill their fiduciary responsibilities and oversight functions.
Some organizations have established dedicated cybersecurity committees within their boards, composed of members with relevant expertise or backgrounds. These committees foster deeper discussions on incident response readiness, emerging threats, and strategic priorities. They also facilitate engagement with external auditors, regulators, and technology partners, ensuring that the board remains fully informed and proactive.
Integrating Incident Response Into Enterprise Risk Management
Incident response planning is increasingly viewed as an integral part of enterprise risk management (ERM). Boards are demanding comprehensive risk assessments that incorporate cyber threats alongside traditional business risks. This holistic perspective allows for better prioritization and resource allocation.
Moreover, boards are encouraging the development of cross-functional incident response teams that include representatives from IT, legal, communications, compliance, and executive leadership. This collaboration ensures that responses are coordinated, timely, and effective in minimizing damage.
The use of simulation exercises and tabletop scenarios has become a best practice in testing and refining incident response plans. Such proactive measures help identify weaknesses and improve organizational resilience before real incidents occur.
Boards are also emphasizing clear incident escalation protocols and communication plans that address both internal stakeholders and external parties such as customers, regulators, and media. Effective communication during a cyber incident can significantly mitigate reputational harm and facilitate regulatory compliance.
In addition, continuous improvement mechanisms, including post-incident reviews and lessons learned sessions, are now embedded within ERM frameworks. Boards oversee these processes to ensure that incident response strategies evolve in line with emerging threats and organizational changes.
Future Trends in Incident Response Governance
Looking ahead, the role of artificial intelligence (AI) and automation in incident response is set to expand. AI-driven tools can enhance threat detection, accelerate response times, and provide predictive analytics that inform strategic decisions. Boards will need to understand these technologies’ capabilities and limitations to guide their adoption effectively.
AI can help identify patterns in large data sets, flag anomalies, and automate routine response actions, freeing human analysts to focus on complex threats. However, reliance on AI also introduces risks, such as false positives, adversarial attacks against AI models, and ethical considerations. Board oversight will be crucial in balancing innovation with risk management.
Furthermore, as remote and hybrid work models become permanent fixtures, incident response plans must adapt to new vulnerabilities and operational realities. Boards will likely emphasize policies addressing endpoint security, cloud infrastructure, and third-party risks.
The proliferation of Internet of Things (IoT) devices, mobile workforces, and cloud-based services expands the attack surface considerably. Incident response strategies must evolve to detect and contain threats across diverse environments and technologies.
Finally, the increasing interconnection of global supply chains means incident response planning must consider external dependencies and potential cascading effects. This complexity reinforces the need for board-level oversight and continuous improvement of cybersecurity strategies.
Boards are expected to demand greater transparency and assurance from suppliers and partners regarding their cybersecurity posture. This may include contractual requirements for incident response readiness and collaborative communication during supply chain disruptions.
Conclusion
The emergence of incident response planning as a boardroom-level conversation reflects the evolving nature of cybersecurity threats and the critical need for strategic oversight. Boards now play a decisive role in shaping how organizations prepare for, respond to, and recover from cyber incidents. By partnering with expert technology firms and integrating incident response into enterprise risk management, businesses can strengthen their resilience and protect their long-term success.
As cyber threats continue to evolve, sustained board engagement and informed governance will remain indispensable in safeguarding enterprise assets and reputation. The collaborative efforts of IT professionals, external partners, and executive leadership will define the future of incident response and organizational security.
Ultimately, the alignment of incident response planning with corporate strategy ensures that cybersecurity is not an isolated technical challenge but a fundamental aspect of business continuity and value preservation. Boards that embrace this responsibility will position their organizations to navigate the complexities of the digital age confidently and securely.